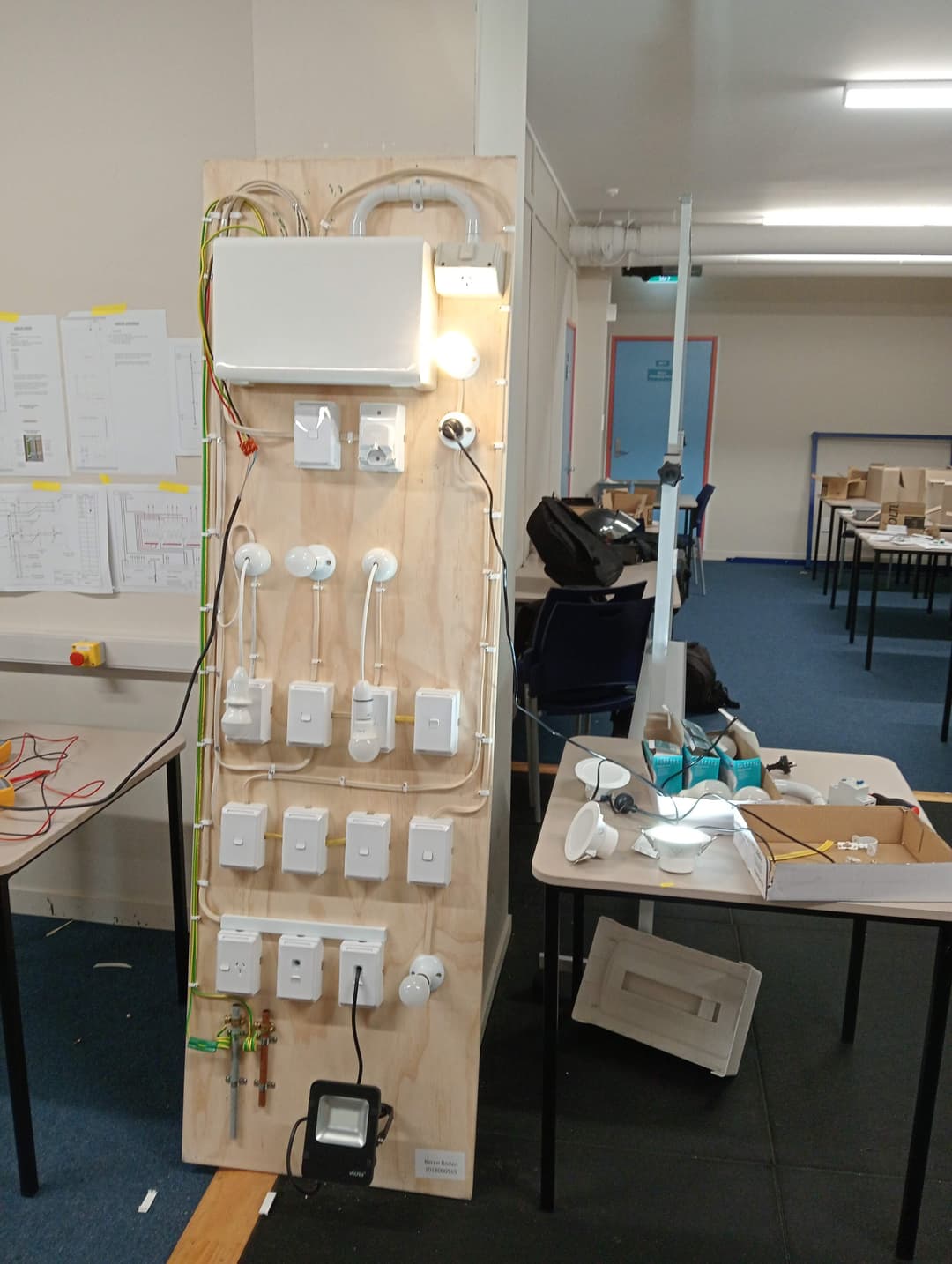
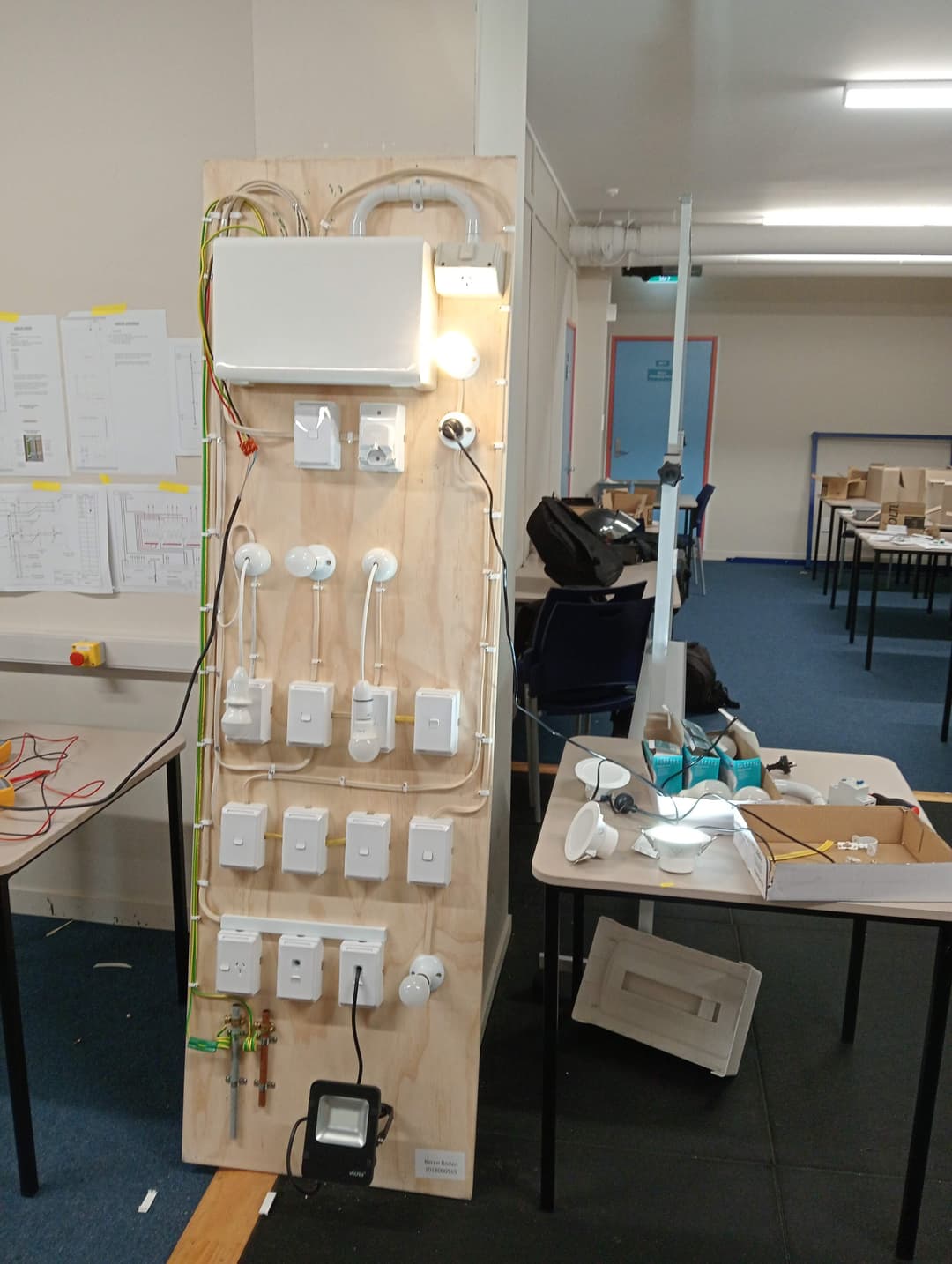
Many practical subjects covered in this course has added much value in part-time work as a junior security technician with Advanced Security. ----> Learning about relays helped me understand how to wire inputs and outputs for exit buttons, EDRs, PIRs, mag clamps, and electronic locks. Understanding how circuits are wired in series and parallel, aided in successfully wiring an EDR's N/C relay in series with an auto-door open relay to unlock the door. Building many small circuits, and a basic domestic circuit, I could see the materials and tools both security technicians and electricians require to carry out the work efficiently.